AWS Organizations
This guide explains how to add an AWS Organization to Cloudaware and enable the auto-discovery of organizational member account within AWS Organization.
Summary
To integrate AWS Organization with Cloudaware:
Add the AWS Organization Management Account to Cloudaware using an AWS IAM Role.
Create a CloudFormation stack in AWS using the Cloudaware СF template:
CloudAware Role Name: replace
auto-generatewith a relevant name, e.g. CloudawareRoleExternal ID: generate in Cloudaware
Create AWS CloudFormation StackSet in AWS Organization for auto-collection of member accounts.
Create a CloudFormation stackset in AWS using the Cloudaware CF template:
CloudAware Role Name: replace
auto-generatewith a relevant name, e.g. CloudawareGlobalRoleExternal ID: generate in Cloudaware and save it for step 3
Add AWS Organization to Cloudaware.
IAM Role Name: use the name of the role created for a stackset in step 2
External ID: use the External ID from step 2
See the setup guidelines below for details.
Prerequisites
Ensure that AWS Organizations is in use. Read more
Ensure that
all featuresis enabled in your AWS Organization. NOTE: this action is irreversible! Read moreEnsure that you have registered an account with Cloudaware. Read more
Add AWS Organization Management Account to Cloudaware
Use this guide to learn how to add an AWS Account to Cloudaware using an IAM Role.
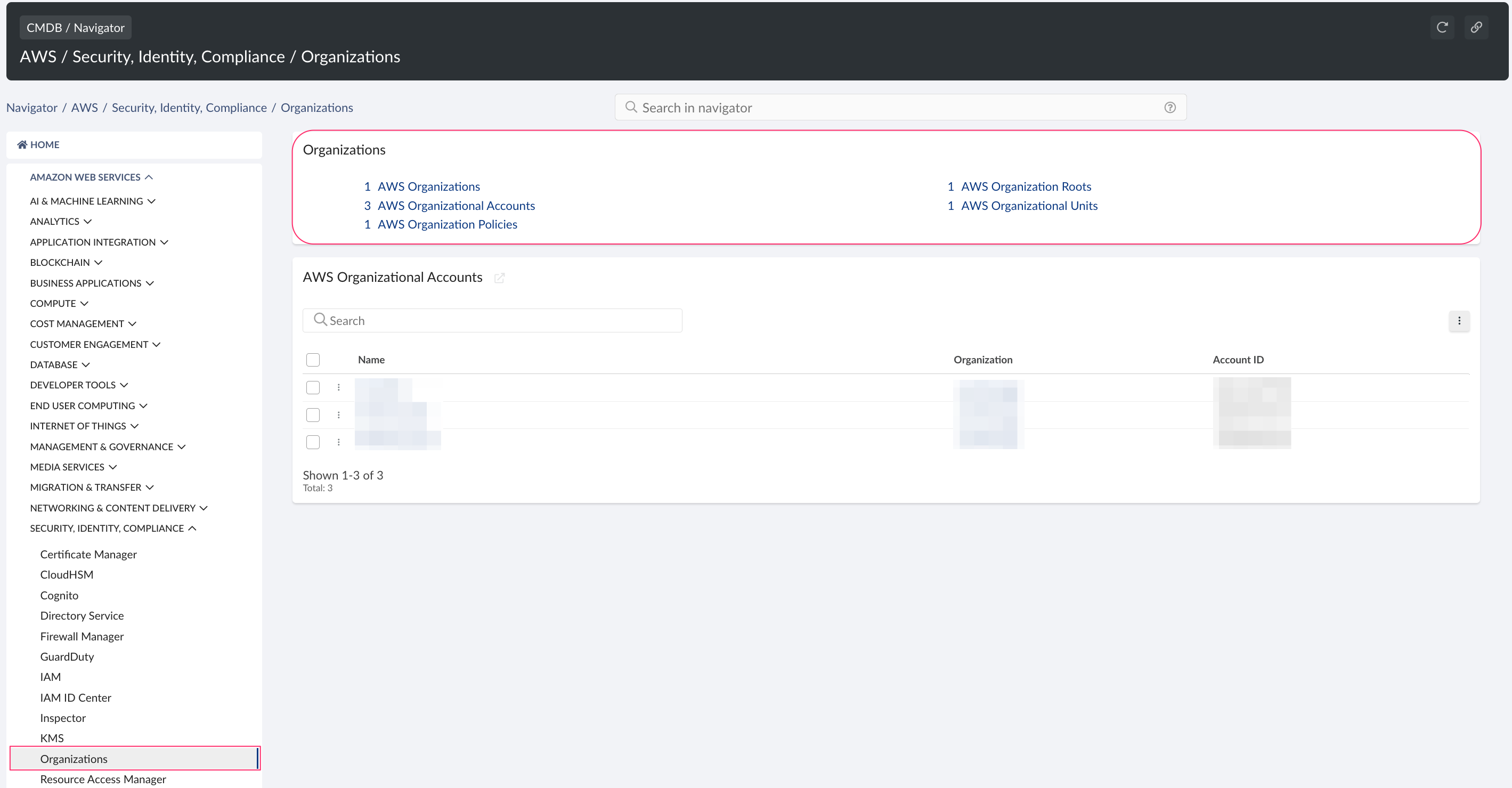
Once the account is added, view AWS Organizations data in Cloudaware CMDB. Go to CMDB Navigator → select AMAZON WEB SERVICES on the left → Security, Identity, Compliance → Organizations:
Create CloudFormation StackSet in AWS Organization
Use AWS CloudFormation StackSets to roll out the Cloudaware CloudFormation stack over multiple AWS accounts in your AWS Organization. This will enable auto-discovery of AWS Organization member accounts in Cloudaware.
Log in to AWS Console. Select All Services → section Management & Governance → CloudFormation → StackSets.
Click Create StackSet.
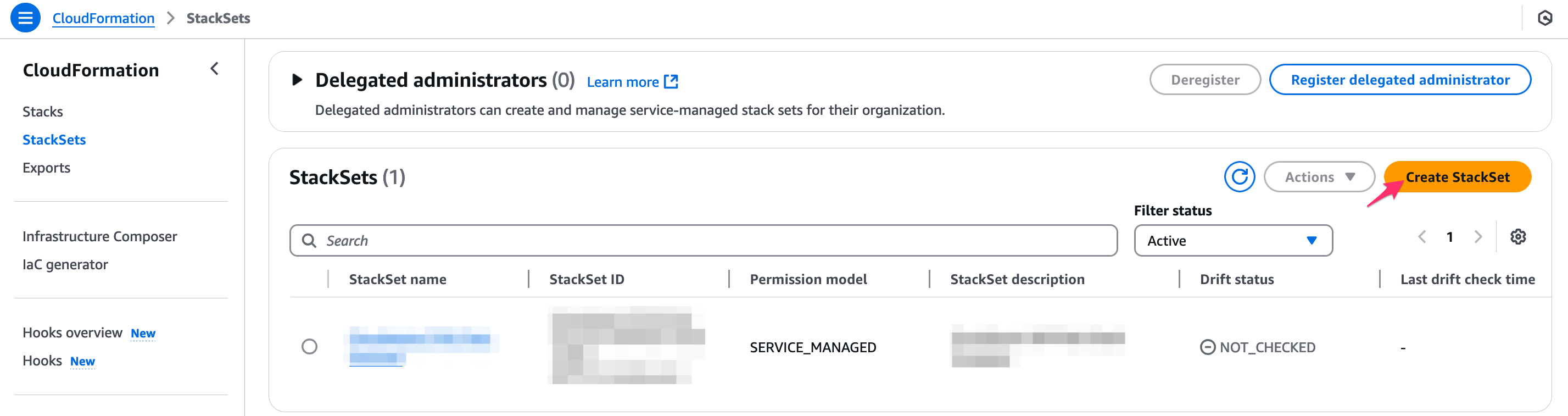
Select 'Service-Managed Permissions'.
If you prefer using Self-Managed permissions, set up:
AWSCloudFormationStackSetAdministrationRole in the administrator account using the template https://s3.amazonaws.com/cloudformation-stackset-sample-templates-us-east-1/AWSCloudFormationStackSetAdministrationRole.yml
AWSCloudFormationStackSetExecutionRole which trusts the root account in each(!) target account using the template https://s3.amazonaws.com/cloudformation-stackset-sample-templates-us-east-1/AWSCloudFormationStackSetExecutionRole.yml
Read more
Select 'Template is ready' → 'Upload a template file'. Click Choose file and upload the Cloudaware CloudFormation template used when adding the AWS Organization Management account and creating a stack.
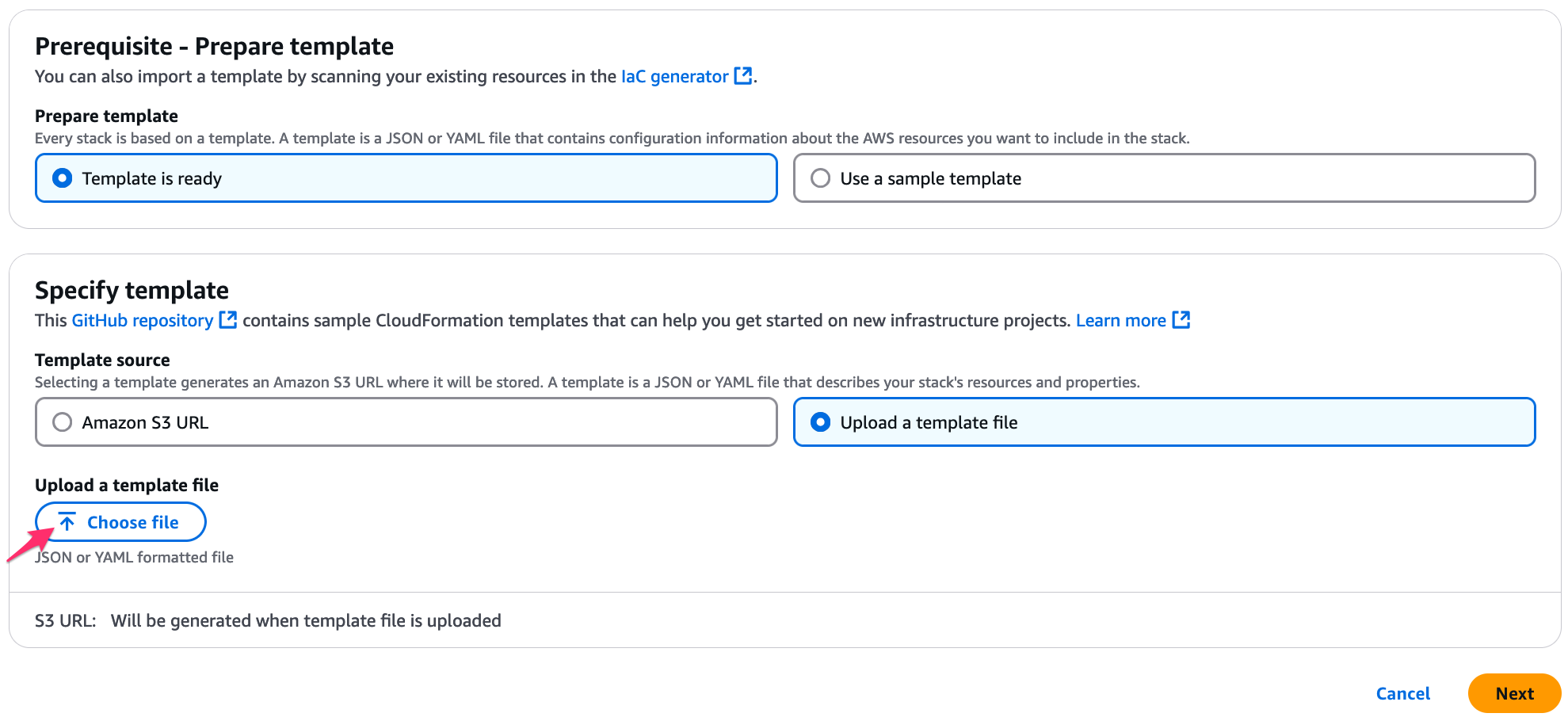
Click Next.Provide a meaningful name to the stackset. Replace
auto-generatein CloudAware Role Name with a custom name*, e.g. CloudawareGlobalRole. Insert External ID** used for adding AWS Organization Management Account to Cloudaware.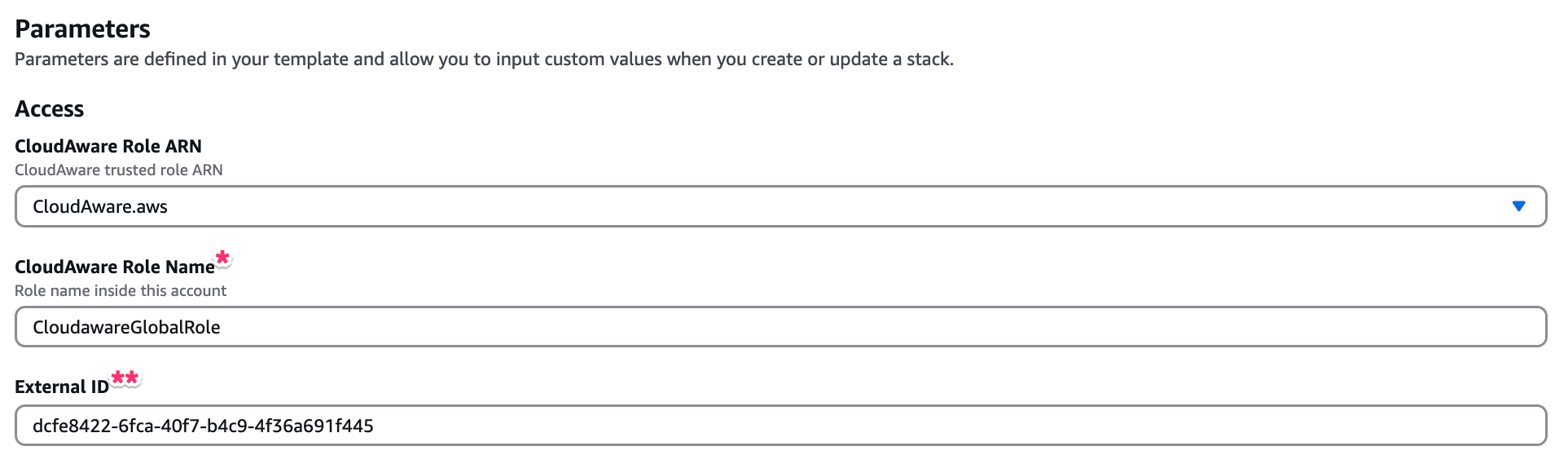
Note that these IAM Role Name and External ID are required for adding an AWS Organization to Cloudaware.
Set up the policies. Click Next.
Configure StackSet options, such as tags and execution configuration. Check the box I acknowledge that AWS CloudFormation might create IAM resources with customised names.
Set deployment options.
You can limit the stackset deployment to specific Organization Units to limit account discovery in the AWS Organization. Learn more on how to specify the OUs as deployment targets.
IMPORTANT: If a specific Organization Unit (OU) is already onboarded by Cloudaware and you would like to add one or more additional OUs, create a StackSet with new OU(s) specified, using exactly the same Role Name and External ID that were used when adding the first OU.
Click Next.
Review the StackSet details. Click Submit. Allow some time for the StackSet to be created.
Please allow some time for the StackSet to be created.
Add AWS Organization to Cloudaware
Log in to Cloudaware → Admin.
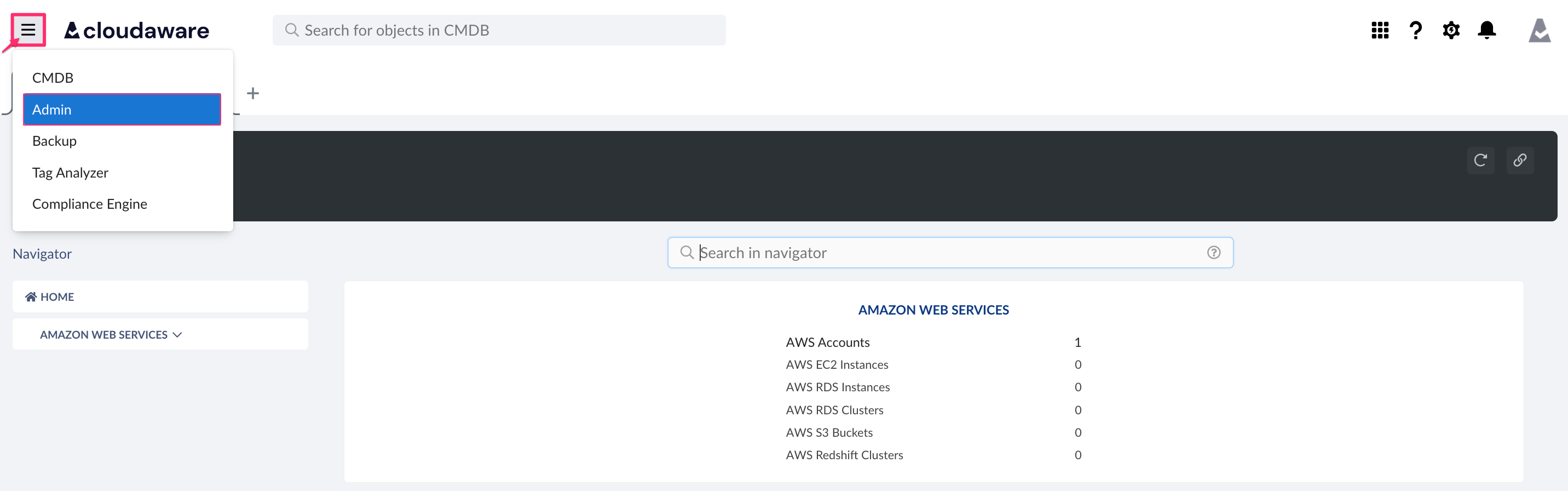
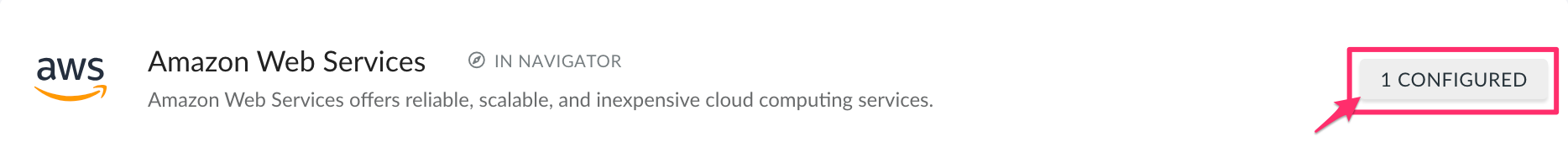
Find Amazon Web Services. Click +N CONFIGURED.
Select the tab 'Organizations' → +ADD AWS ORGANIZATION.
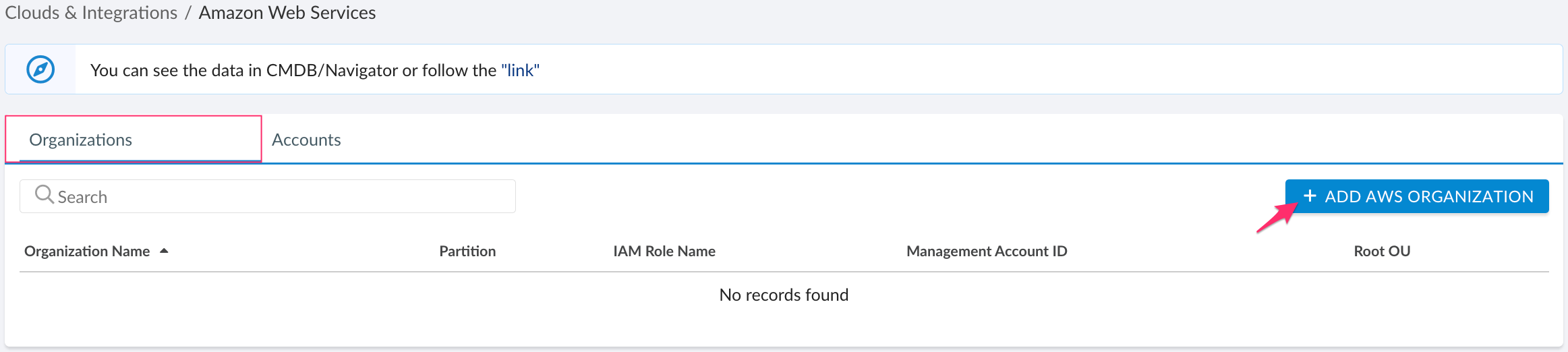
Fill out the form:
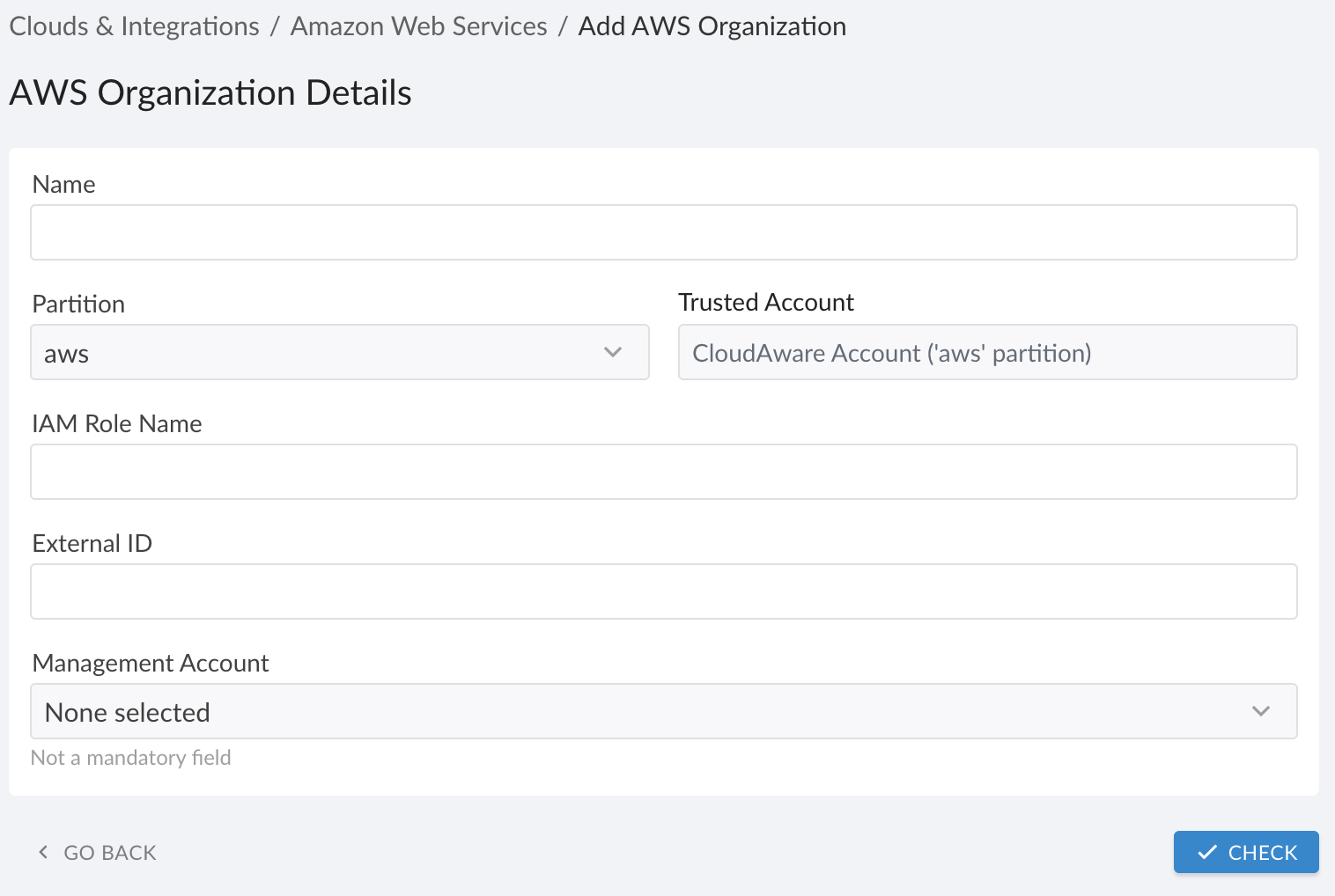
WHERE
Name – provide a meaningful AWS Organization name
Partition – select the partition of AWS Organization Management Account (Public Cloud is pre-selected asawsby default)
IAM Role Name – insert the name of Cloudaware IAM Role that was used when creating a stackset in AWS Organization
External ID – insert the External ID that was used for creating stackset in AWS Organization Management Account
Management Account – select the AWS Organization Management Account from the listClick CHECK. Once validation is passed, click SAVE.
Please allow some time for Cloudaware to automatically collect AWS Organizational member accounts.
Update External ID for AWS Accounts Moved Between Organizations
If you have moved an AWS account from one AWS Organization to another, update the External ID in Cloudaware as follows:
Log in to Cloudaware → Admin.
Select Amazon Web Services → N CONFIGURED.
Locate the affected AWS account in the list. Click the three-dot menu → Edit.
Update the External ID and Role ARN using the values from the CloudFormation stack in the new AWS Organization.
Click CHECK to test the connection. Click SAVE.