Patch Management - Overview
This page provides an overview of Cloudaware’s Patch Management capabilities.
About
Cloudaware offers a low-friction, high-value continuous patching. Cloudaware’s approach is to ensure a customer’s compute instances are patched in a timely manner without causing harm and interference to production applications.
Features
Cloudaware Patch Management supports capabilities such as automatically generated release notes, full and partial rollback, and deployment of emergency patches for critical security vulnerabilities.
Transparency
Cloudaware provides a detailed report indicating available upgradable packages, the machines that will be updated, and the scheduled patch installation date. This gives customers sufficient time to evaluate whether some patches should be applied manually or excluded from the scope.
Consistency
Cloudaware generates a patching snapshot defining the upgradable packages and versions to which they will be updated. Cloudaware guarantees this snapshot to be implemented across all environments such as Dev, QA, Staging and Prod. If any patch is detected as manually upgraded or auto-installed, Cloudaware will skip it.
Cloudaware also supports patch groups, meaning that only members of one patch group will be rebooted at a time if necessary.
Rollback
To undo a failed patch release, customers can address Cloudaware's rollback script available by default. The rollback script is located on every patched instance in the following location: /opt/breeze-agent/os_updater/YYYYMMDDhhmmss.sh
Cloudaware can perform a simultaneous rollback in all instances within a given cloud account. If rollback is requested, Cloudaware’s Breeze agent will set repo to the previous GUID, execute the rollback script and verify rollback using yum update against preview repo GUID. After the script execution is complete, the yum update should not introduce any changes to the packages on the host.
Emergency Security Release
If a critical security vulnerability is identified, Cloudaware will create an emergency release. The emergency release will contain security patches and potentially other updates that have accumulated since the last release.
Patch Information in CMDB
Cloudaware provides patch monitoring and patch eligibility information in CMDB. Along with OS level data, the information on patches becomes available in Cloudaware CMDB once Breeze agent is installed on a machine.
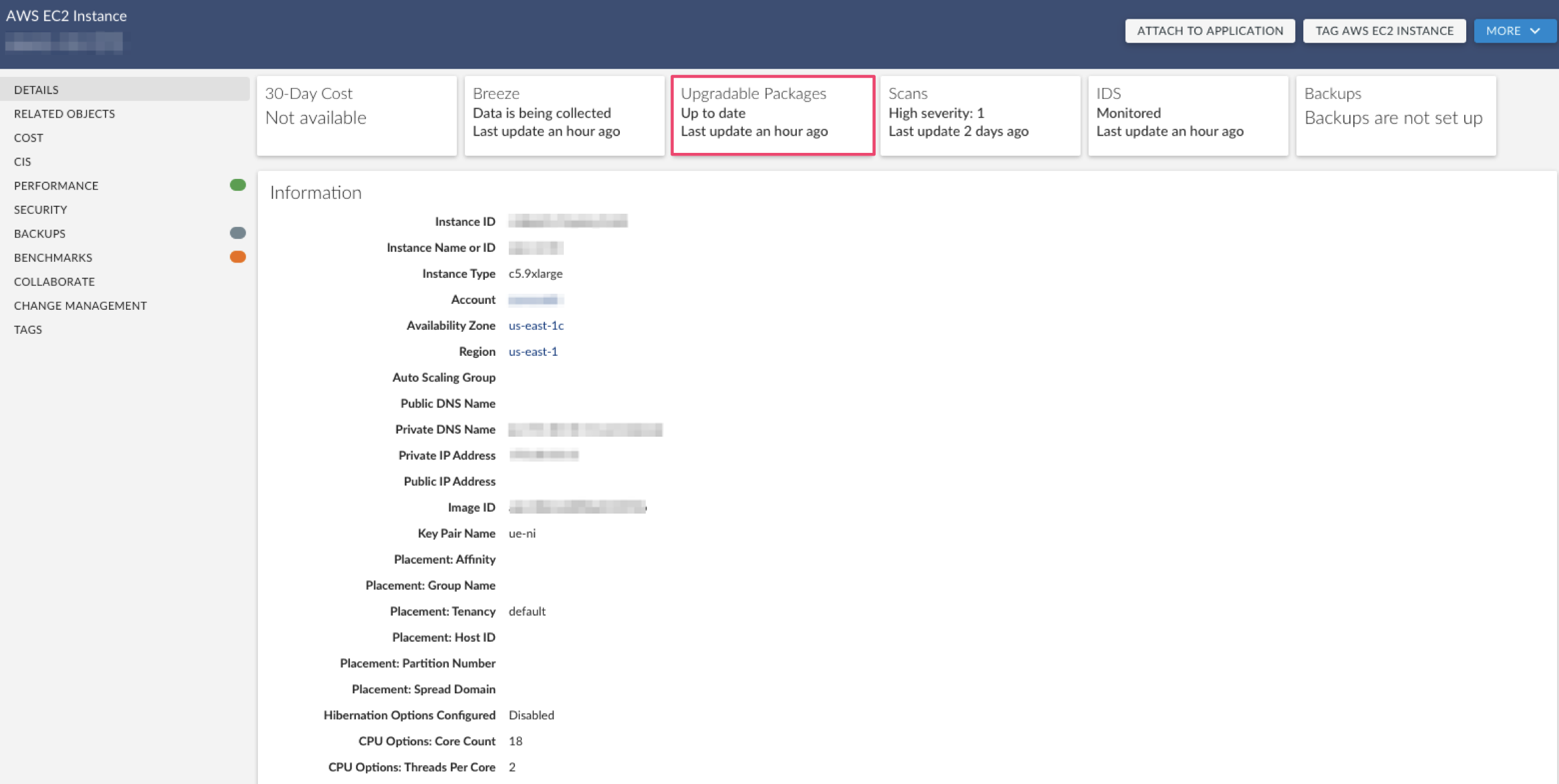
Cloudaware shows what patches are outstanding, equally well for Windows and Linux. If a patch is security-related, meaning that there is a security vulnerability that has been identified with that version of the package, the checkbox 'Security' is going to be checked requiring your attention.
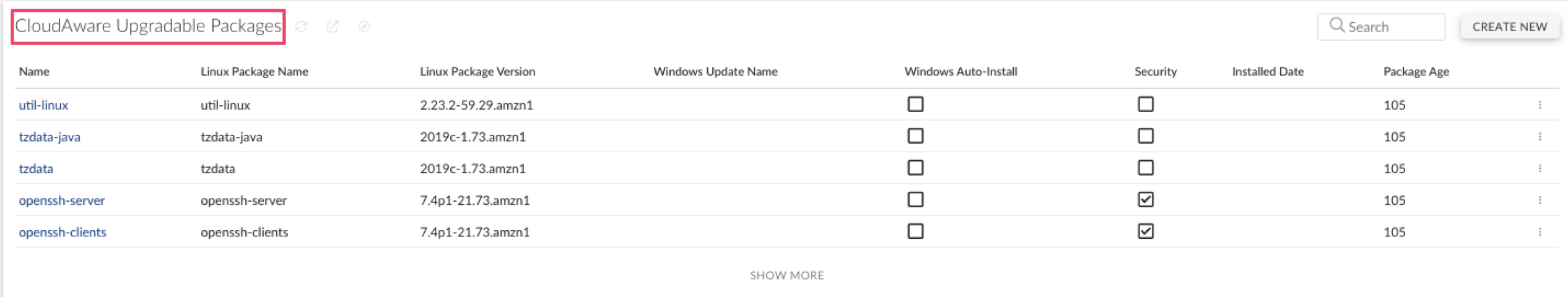
Once a package is applied, the column 'Installed Date' is populated. The column 'Package Age' demonstrates how well the customer’s security team is doing with patching.
List of supported objects
Cloudaware supports the following patching-related objects (with API names):
CloudAware Linux Package
CA10__CaLinuxPackage__cCloudAware Upgradable Package
CA10__CaUpgradablePackage__c