Backup & Replication - How-To
EC2 Instance Backup
Enable EC2 Instance Backup
Sign in to your Cloudaware account. Go to Admin → Backup. To set up a global backup policy, go to the "Settings" tab and select the account.
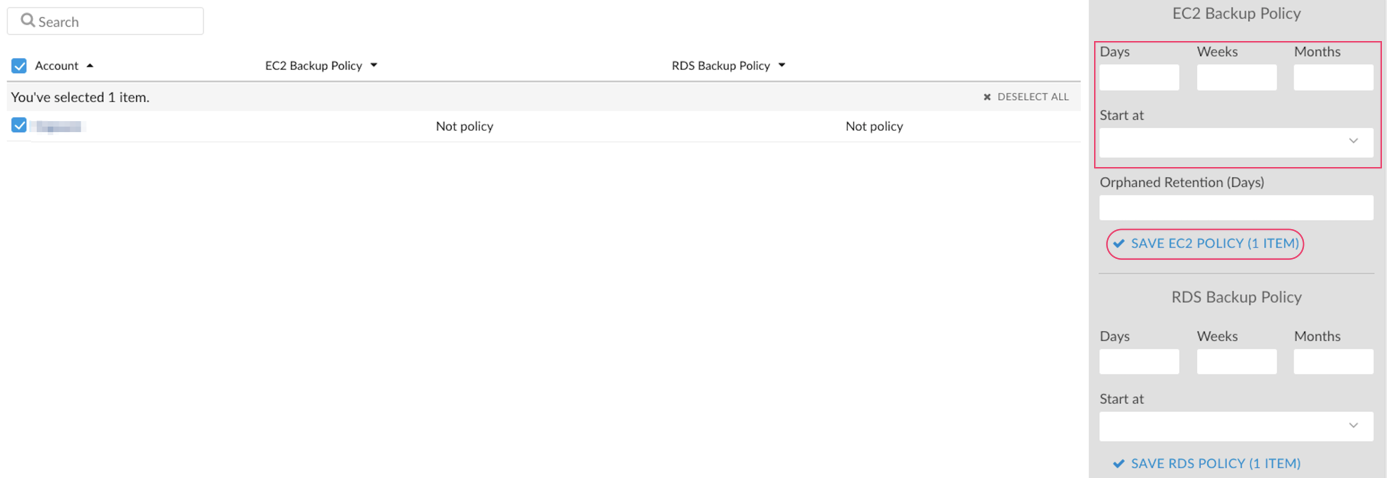
To enable scheduled backups, select the time backups will start on from the list in 'Start at'.
A backup task will back up all non-terminated instances, including instances in a 'stopped' state.
You can also select any instance from the list under the 'EC2 instances' tab and set the backup policy for it. This will override the global backup policy set on the account.
Disable EC2 Instance Backup
To disable scheduled backups for EC2 Instance, select the instance under question and click ''Remove Policy'':
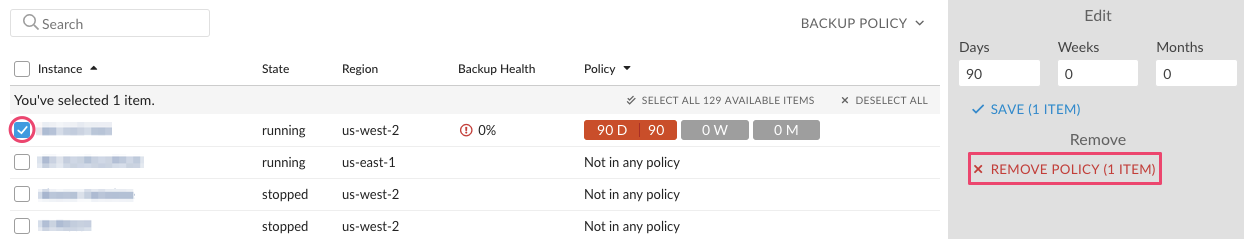
Existing backups will be stored until they expire according to the backup policy rules. If an instance is terminated, backups are stored as well until they expire.
Backup Metadata
AMI Description will contain the following information about the original instance from which a backup is taken:
Instance ID
Key
Security Group(s)
Instance Type
Availability Zone
Public IP Address
In addition AMI will contain 2 backups tags:
Instance ID
Policy Type
Cost allocation tags can be applied to AMIs as well. Contact support@cloudaware.com for additional details.
View EC2 Instance Backup Status
By looking at any instance in Cloudaware, we can tell what backup policies are in effect and check their status.
The following fields mark the backup policy and the backup status:
Daily Backups (the number of daily snapshots specified by the policy)
Daily Backups Status (the actual number of available consecutive AMIs starting from today's date)
For example, today is the 10th day of a month and Daily Backups field has value of 7 but Daily Backup Status has value of 3. It means that Cloudaware only found backups for the last 3 days and the backups for the other 4 days that should be there are not present. Whenever the backup policy does not equal the backup policy’s status, a backup is missing
- Weekly Backups
Weekly Backups Status
Monthly Backups
Monthly Backups Status
In order to view EC2 Instance backups, navigate to an instance of choice.Scroll down until you see a related list called EC2 Instance Backups.
Backup Tags
EC2 backup functionality relies on AWS tags to advise the backup scheduled task on how an instance should be backed up.
- AWS backup tag name is: gig-backup
AWS backup tag value is: Nd-Nw-Nm, where N is number of days/weeks/months
For example, a backup policy 3d-10w-12m creates daily backups every day and rotates them over the period of 3 days, a weekly backup which will be rotated over 10 weeks and a monthly backup which will be rotated over 12 months. Hyphens can be omitted.
Examples of valid backup tag values:
1. 3d-10w-12m
2. 4d10w12m
3. 3d-10w
4. 3d
5. 3
3 and 4 are equivalent due to backwards compatibility.
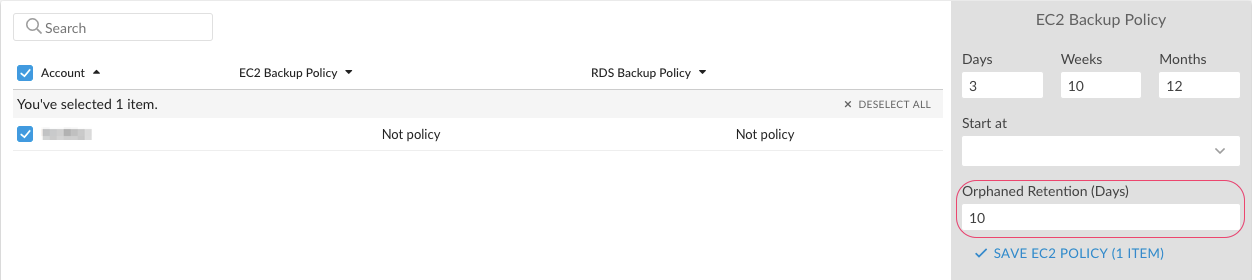
Enable Orphaned Backup Retention
The Orphaned Backup Retention allows to manage an AMI clearing process. When setting up the global backup policy, insert the number of days in the 'Orphaned Retention (Days)' field. For example, Orphaned Retention = 10 means that backups will be deleted 10 days after the source instance is terminated:
EC2 Images Replication
To enable EC2 images replication, add the tag gig-replicate in the following format to an instance:
- AWS backup tag name is: gig-replicate
- AWS backup tag value is: N@REGION (multiple policies should be separated by semicolon) where N is a number of images to replicate and REGION is the destination region.
For example, a replication policy 2@us-west-1; 3@us-west-2 will replicate 2 latest AMIs of the instance to the us-west-1 region and 3 AMIs - to the us-west-2.
Examples of valid replicate tag values:
10@us-west-1
5@us-west-2; 3@eu-west-1
RDS Instance Backup
RDS Instance backup works exactly the same as EC2 Instance Backup described above with one exception: RDS Snapshots only have tag-based metadata.
S3 Bucket Backup
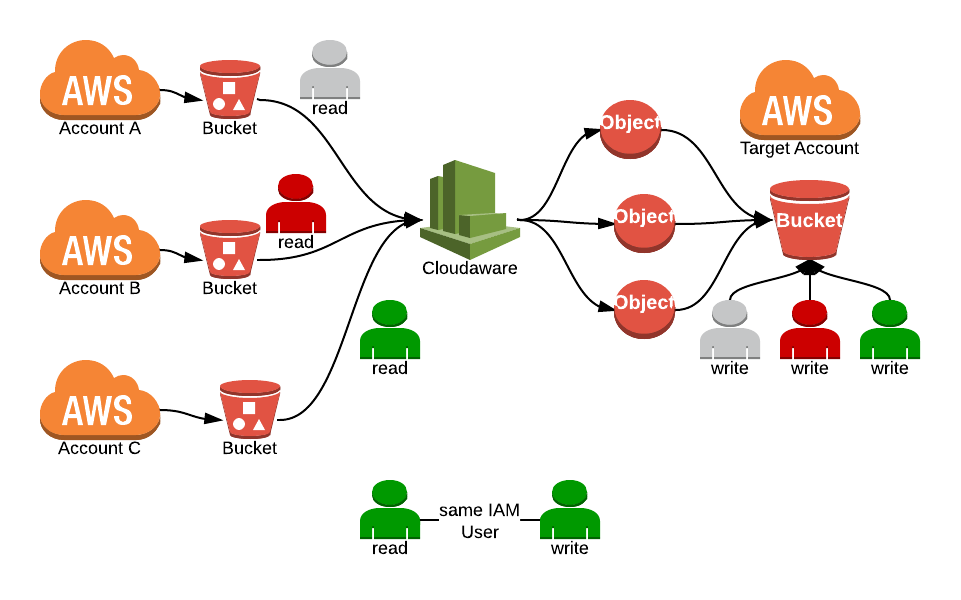
S3 buckets can be backed up to another S3 bucket within the same or another AWS account. Both source and target accounts have to be added to Cloudaware.
CloudAware IAM user which is used to access the source bucket must have write access to the target bucket in the target AWS account.
S3 Backups are using tags. The buckets that need to be backed up must have tags applied in the following format: 1d0w0m@cf-templates-1ajskw0nz6e8-us-east-1
- AWS backup tag name is: gig-backup
- AWS backup tag value is: Nd-Nw-Nm@BucketName
For example, the tag 1d0w0m@mybucket takes the source bucket and copies its content to the target bucket once a day.
Cloudaware creates a directory gig-backup in the target bucket. Inside this directory you can see directories for each source bucket.
Cloudaware automatically deletes folders with data that falls outside the backup policy retention criteria.
Create a target bucket.
Apply the following IAM policy to the target bucket.
BUCKET_NAME is the target bucket. It is assumed that a Cloudaware user already has access to the source buckets.
Ensure that every source Cloudaware account is granted access to the target bucket.
{
"AWSTemplateFormatVersion" : "2010-09-09",
"Description" : "Backup Bucket Policies",
"Resources" : {
"S3BucketPolicy" : {
"Type" : "AWS::S3::BucketPolicy",
"Properties" : {
"Bucket" : "BUCKET_NAME",
"PolicyDocument" : {
"Statement" : [
{
"Principal" : { "AWS" : [
"arn:aws:iam::ACCOUNT_ID_A:user/CloudawareIAMUserA",
"arn:aws:iam::ACCOUNT_ID_B:user/CloudawareIAMUserB"
] },
"Resource" : [ "arn:aws:s3:::BUCKET_NAME" ],
"Effect" : "Allow",
"Action" : [ "s3:List*" ]
},
{
"Principal" : { "AWS" : [
"arn:aws:iam::ACCOUNT_ID_A:user/CloudawareIAMUserA",
"arn:aws:iam::ACCOUNT_ID_B:user/CloudawareIAMUserB"
] },
"Resource" : [ "arn:aws:s3:::BUCKET_NAME/*" ],
"Effect" : "Allow",
"Action" : [ "s3:Get*", "s3:Put*", "s3:Delete*" ]
}
]
}
}
}
}
}